
Discover what is iac management and its benefits for IT.
March 12, 2026|8:00 AM
Unlock Your Digital Potential
Whether it’s IT operations, cloud migration, or AI-driven innovation – let’s explore how we can support your success.

March 12, 2026|8:00 AM
Whether it’s IT operations, cloud migration, or AI-driven innovation – let’s explore how we can support your success.
In the rapidly evolving landscape of modern IT, managing infrastructure efficiently is paramount. As organizations shift towards cloud-native architectures and DevOps practices, the traditional manual configuration of servers and networks becomes unsustainable. This is where Infrastructure as Code (IaC) steps in, transforming how we define and provision computing resources. Understanding what is iac management? is crucial for anyone involved in modern IT operations and development.
This comprehensive guide will walk you through the definition of infrastructure as code management, its core principles, and practical steps for effective implementation. We will explore the purpose of IaC management and delve into how IaC works within a managed framework. By the end of this article, you will have a solid introduction to IaC management and a clear grasp of its significant benefits.
Infrastructure as Code (IaC) represents a revolutionary approach to managing IT infrastructure. Instead of manually configuring hardware and software, IaC uses code to define, provision, and manage infrastructure resources. This includes virtual machines, networks, databases, load balancers, and more. The fundamental idea is to apply software development best practices to infrastructure operations.
This method allows infrastructure to be treated like any other software component, making it versionable, testable, and deployable through automated processes. The benefits are substantial, including increased consistency, reduced human error, and faster deployment cycles. It shifts infrastructure configuration from a manual, error-prone task to an automated, repeatable process.
IaC leverages declarative or imperative languages to describe the desired state of infrastructure. Declarative approaches focus on what the infrastructure should look like, while imperative approaches specify how to achieve that state. Tools like Terraform and AWS CloudFormation are examples of declarative IaC, defining the end state of resources.
When we talk about what is iac management?, we are referring to the comprehensive set of practices, tools, and processes used to effectively control, secure, and optimize your Infrastructure as Code. It’s not just about writing IaC; it’s about managing the entire lifecycle of your infrastructure definitions. This involves ensuring consistency, compliance, security, and efficiency across all your environments.
The purpose of IaC management is to bring order and governance to your IaC efforts, preventing configuration drift and enhancing operational reliability. Without proper management, IaC can quickly become unwieldy, leading to inconsistencies, security vulnerabilities, and deployment failures. It transforms raw IaC files into a robust, maintainable system.
At its heart, IaC management addresses the inherent challenges of managing vast and dynamic infrastructure defined in code. It provides a structured framework for teams to collaborate, deploy, and maintain their infrastructure definitions with confidence. This robust approach ensures that your infrastructure remains aligned with your organizational goals and security policies.

Explaining IaC management also involves recognizing that while IaC automates provisioning, management automates the management of that automation. It encompasses everything from the initial creation of IaC templates to their continuous operation and eventual decommissioning. This holistic view ensures that IaC delivers on its promise of reliable and scalable infrastructure.
Effective IaC management relies on several crucial pillars that ensure your infrastructure remains robust, secure, and consistent. These components work together to provide a comprehensive framework for controlling your code-defined infrastructure. Understanding these fundamentals of IaC is essential for successful implementation.
Version control is arguably the most critical pillar for IaC management, leveraging systems like Git. It treats infrastructure code like any other software code, allowing teams to track changes, revert to previous versions, and collaborate effectively. This ensures an auditable history of all infrastructure modifications. Each change is documented, providing a clear trail for troubleshooting and compliance.
Using branches for new features or environment changes prevents conflicts and allows for structured development. Pull requests enable code reviews, enhancing quality and catching errors before deployment. This practice is fundamental to understanding IaC principles and maintaining control.
Just as application code is rigorously tested, IaC code requires thorough testing and validation. This pillar involves linting, unit tests, integration tests, and end-to-end tests to ensure that infrastructure definitions behave as expected. Testing prevents faulty configurations from reaching production environments. Automated tests can check for syntax errors, validate resource properties, and even simulate deployments.
Tools like Terratest for Terraform or Pester for PowerShell DSC provide frameworks for writing these tests. Integrating testing into your CI/CD pipeline ensures that every code change is validated automatically. This greatly reduces the risk of infrastructure failures and security vulnerabilities.
Security and compliance are non-negotiable aspects of IaC management. This pillar focuses on embedding security policies directly into your IaC templates and enforcing compliance standards throughout the deployment process. It involves scanning IaC for vulnerabilities and misconfigurations before provisioning. Examples include ensuring storage buckets are not publicly accessible or that network security groups adhere to least privilege principles.
Tools like Checkov, InSpec, or custom policy engines help identify and remediate security risks proactively. Integrating these checks into your CI/CD pipeline ensures that no non-compliant infrastructure can be deployed. This proactive approach strengthens your overall security posture and simplifies audit processes.
Configuration drift occurs when the actual state of your infrastructure diverges from its defined state in your IaC templates. This can happen due to manual changes, out-of-band updates, or errors. Drift detection tools continuously monitor your deployed infrastructure and compare it against your IaC definitions. This comparison helps identify discrepancies.
Upon detecting drift, the system can either alert operators or automatically remediate the issue by reapplying the correct IaC configuration. This ensures that your infrastructure remains consistent with your desired state, preventing unexpected behavior and security gaps. It’s a core component of how IaC works in a mature environment.
Managing sensitive information, such as API keys, database credentials, and certificates, within IaC is critical. This pillar involves using dedicated secrets management solutions like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault. These tools securely store and distribute secrets to infrastructure components at runtime. Never hardcode secrets directly into your IaC templates.
Integrating secrets management ensures that sensitive data is encrypted at rest and in transit, and access is tightly controlled. This protects your infrastructure from unauthorized access and prevents credentials from being exposed in code repositories. It’s a vital security measure in any IaC strategy.
Once infrastructure is deployed via IaC, continuous observability and monitoring are essential. This pillar involves collecting logs, metrics, and traces from your infrastructure components to gain insights into their performance and health. Monitoring tools can track resource utilization, network traffic, and application performance. This information helps in identifying issues promptly.
Setting up alerts for anomalies and critical events allows for proactive incident response. Integrating monitoring solutions with your IaC deployments ensures that every new resource comes with built-in visibility. This comprehensive approach helps maintain the reliability and performance of your automated infrastructure.
Implementing effective IaC management requires a structured approach. These steps provide a practical guide for establishing robust processes and leveraging the full potential of your Infrastructure as Code. This section details the practical how-to aspect of what is iac management?
Before writing any code, thoroughly define your infrastructure needs. Document the types of resources required, their configurations, network topology, and security policies. Engage with all stakeholders—developers, operations, and security teams—to gather comprehensive requirements. This foundational step ensures your IaC solutions align with business needs.
Clear requirements will guide your choice of IaC tools and architecture. They help prevent scope creep and ensure that the infrastructure provisions correctly the first time. A well-defined blueprint simplifies subsequent development and testing phases.
Selecting the right IaC tools is crucial for your management strategy. Popular choices include Terraform (cloud-agnostic), AWS CloudFormation, Azure Resource Manager, Google Cloud Deployment Manager, Ansible, Puppet, and Chef. Evaluate tools based on your cloud environment, team’s existing skill set, and specific feature requirements. Consider factors like declarative vs. imperative approaches and community support.
Each tool has its strengths and weaknesses, so a careful evaluation is necessary. Some organizations might even opt for a hybrid approach, using multiple tools for different layers of their infrastructure. The chosen toolset forms the core of your IaC ecosystem.
Implement a robust version control system, such as Git, for all your IaC code. Create a well-defined branching strategy (e.g., GitFlow, GitHub Flow) to manage changes and collaborations. Ensure that all infrastructure code is committed, reviewed, and approved before deployment. This maintains an audit trail and prevents unauthorized modifications.
Treat your IaC repositories with the same rigor as your application code repositories. Enforce proper commit messages and pull request workflows. This is a fundamental aspect of the definition of infrastructure as code management, ensuring traceability and accountability.
Integrate automated testing into your IaC development pipeline. This includes linting to check code style, static analysis for potential issues, and unit/integration tests to validate resource configurations. Use specialized IaC testing frameworks where available. Ensure that no infrastructure code is deployed without passing these tests.
Consider implementing a “dry run” or plan stage as part of your deployment process. This allows you to preview the changes your IaC will make before they are applied. This proactive testing dramatically reduces the risk of errors and unexpected behavior in production.
Embed security and compliance checks directly into your IaC development and deployment pipeline. Use tools that scan IaC templates for misconfigurations, vulnerabilities, and deviations from security baselines. Define clear security policies and ensure your IaC adheres to them from the outset. This “shift-left” approach to security is critical.
Regularly review and update your security policies to reflect the latest threats and compliance requirements. Automate these checks as much as possible to ensure continuous adherence. This proactive security integration is a key component of understanding IaC principles.
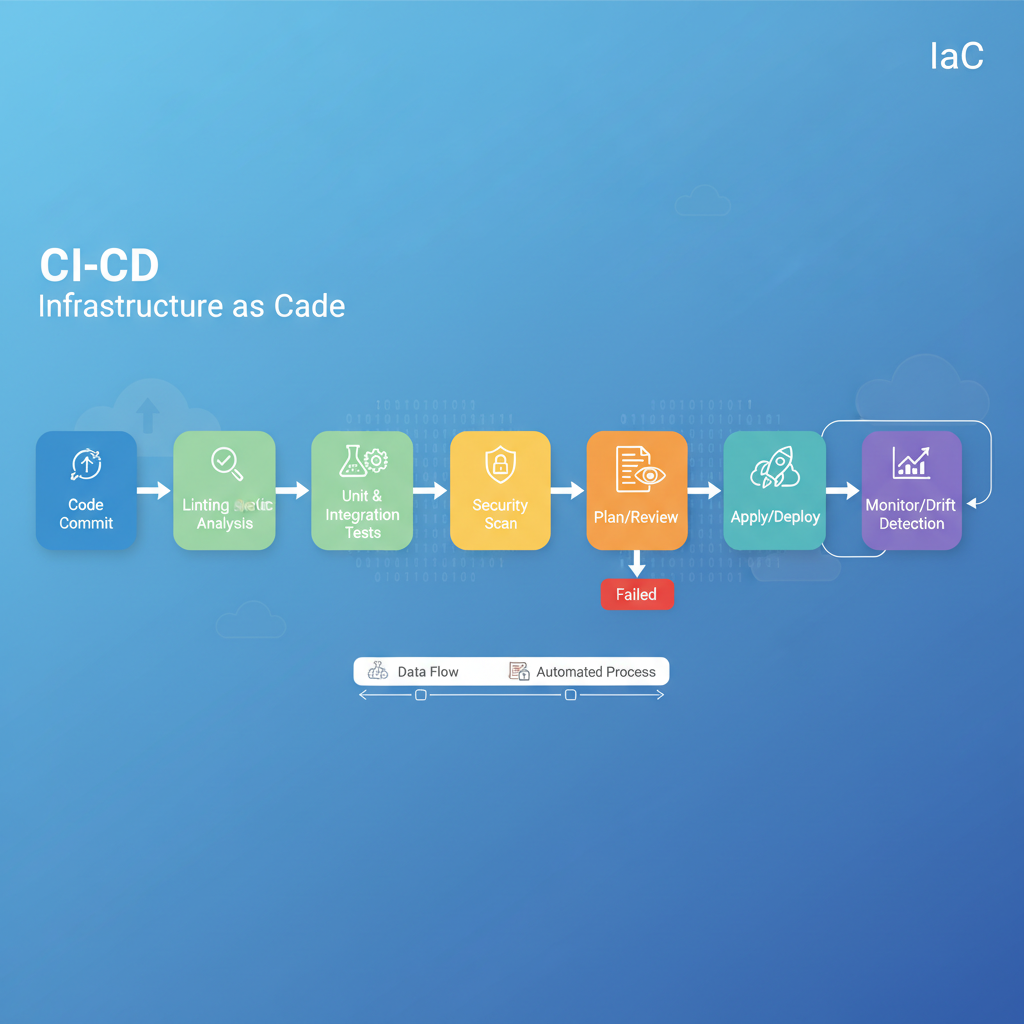
Leverage Continuous Integration/Continuous Deployment (CI/CD) pipelines to automate the deployment of your IaC. Once IaC code is approved and passes all tests, it should be automatically deployed to the target environment. This ensures consistency and reduces manual intervention. Configure monitoring and logging for your deployed infrastructure.
Implement alerting mechanisms to notify teams of performance issues, security incidents, or configuration drift. Use dedicated tools for observability to gain deep insights into your infrastructure’s health and operational status. Automated deployments coupled with robust monitoring are central to the purpose of IaC management.
IaC management is an ongoing process. Regularly review your IaC code, deployment processes, and monitoring data to identify areas for improvement. Implement drift detection mechanisms to identify discrepancies between your desired state (IaC) and the actual state of your infrastructure. Establish procedures for addressing drift, whether through automated remediation or manual intervention.
Foster a culture of continuous learning and collaboration within your team. Encourage sharing best practices and updating documentation regularly. This iterative approach ensures your IaC management strategy remains effective and adaptive to changing needs.
Implementing robust IaC management practices yields significant advantages that extend across an organization’s IT operations. These benefits underscore why so many enterprises are embracing the definition of infrastructure as code management.
One of the primary benefits is unparalleled consistency. By defining infrastructure in code, you eliminate the variability and errors inherent in manual configurations. Every deployment from the same IaC template will result in identical infrastructure. This leads to higher reliability and fewer unexpected issues, a core aspect of explaining IaC management.
IaC management significantly accelerates the provisioning and deployment of infrastructure. Automated pipelines can spin up entire environments in minutes, compared to hours or days with manual methods. This speed is crucial for rapid development, testing, and scaling of applications. It empowers teams to innovate faster.
Embedding security policies directly into IaC templates and validating them through automated checks enhances your overall security posture. Misconfigurations, which are common causes of security breaches, are detected and prevented early in the development cycle. This proactive approach strengthens defenses and reduces attack surfaces.
Automating infrastructure provisioning and management reduces the need for extensive manual labor, freeing up skilled IT staff for more strategic tasks. It also helps optimize resource utilization by allowing for dynamic scaling and precise resource allocation. This translates directly into lower operational costs and increased efficiency.
With all infrastructure defined in version-controlled code, every change leaves an auditable trail. This makes it easier to demonstrate compliance with regulatory requirements and internal policies. Reviewing changes, understanding who made them, and why, becomes straightforward. This transparency is invaluable for governance.
While IaC management offers numerous benefits, it also comes with its own set of challenges. Understanding these hurdles and adopting best practices is key to a successful implementation. The basics of IaC sometimes hide deeper complexities that require careful handling.
The definition of infrastructure as code management refers to the comprehensive set of processes, tools, and practices used to define, provision, configure, and manage IT infrastructure using code, throughout its entire lifecycle. It encompasses version control, testing, security, deployment, and monitoring of the infrastructure definitions themselves.
IaC management enhances security by embedding security policies directly into code, allowing for automated scanning and validation before deployment. This proactive approach helps detect and prevent misconfigurations, ensures compliance with security standards, and reduces the attack surface by enforcing desired states consistently.
Key tools for IaC management vary based on cloud environment and specific needs. Popular choices include Terraform for multi-cloud orchestration, AWS CloudFormation, Azure Resource Manager, and Google Cloud Deployment Manager for cloud-specific IaC. Configuration management tools like Ansible, Puppet, and Chef are also widely used.
The primary purpose of IaC management is to bring control, consistency, and efficiency to the process of provisioning and managing infrastructure. It aims to eliminate manual errors, accelerate deployment cycles, ensure compliance, and prevent configuration drift by treating infrastructure as versioned, testable code.
Yes, IaC management is specifically designed to address and prevent configuration drift. By continuously monitoring the deployed infrastructure and comparing its actual state against the defined state in IaC templates, management tools can detect discrepancies and either alert operators or automatically remediate the drift.
Understanding what is iac management? is no longer a luxury but a necessity for organizations striving for agility, reliability, and security in their IT operations. We’ve explored the foundations of Infrastructure as Code, delved into the core concepts of its management, and outlined the essential pillars for successful implementation. From version control to robust testing and proactive security, effective IaC management transforms how infrastructure is handled.
Embracing these practices leads to improved consistency, faster deployments, enhanced security, and significant cost reductions. While challenges exist, adopting best practices such as modularization, continuous automation, and a strong DevOps culture will pave the way for success. By applying the fundamentals of IaC and adopting a comprehensive management strategy, organizations can build resilient, scalable, and secure infrastructure for the future.
Experience power, efficiency, and rapid scaling with Cloud Platforms!